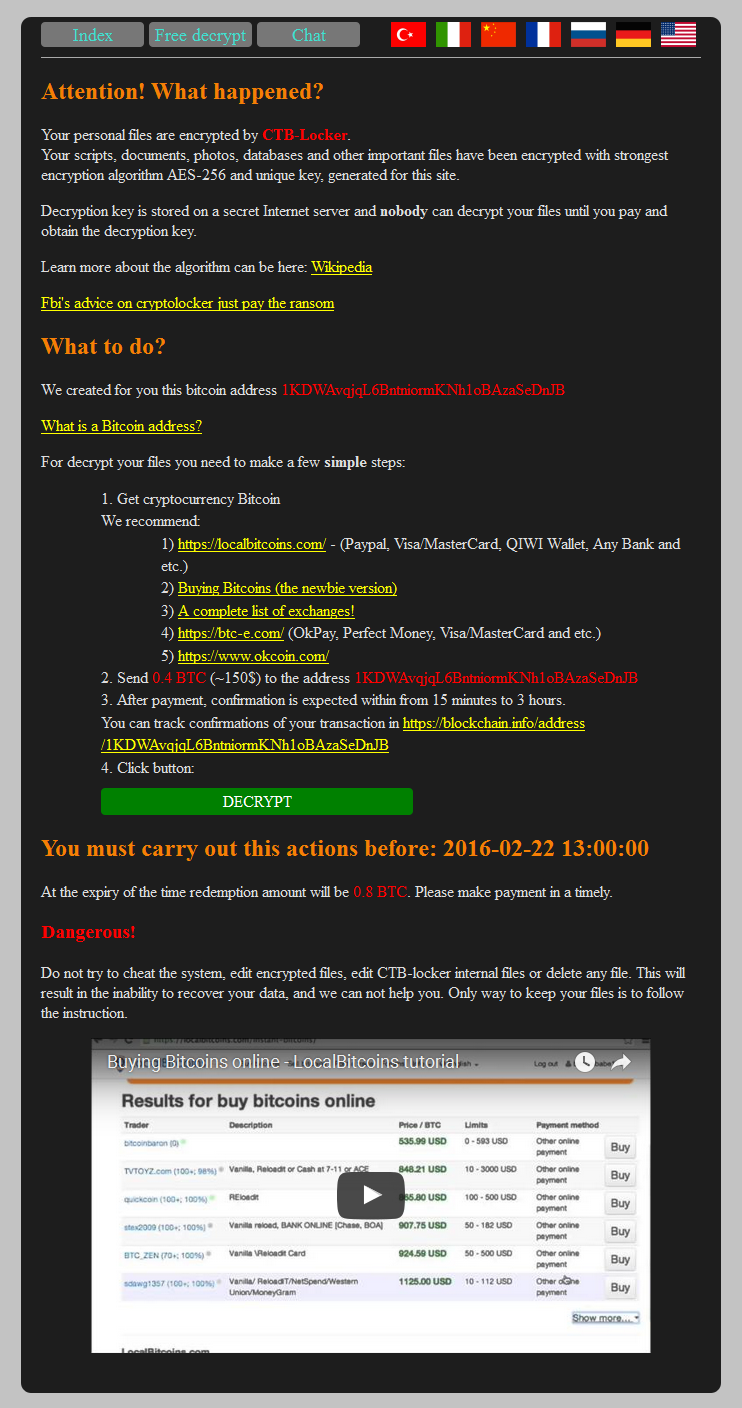
Do you know what ransomware is? It’s a computer compromise, typically spread via a macro in a Microsoft Word file. Those spam “invoices” you get, with a .doc attachment? They’re almost always ransomware. If the macro is run, most of the document and image files on your computer are encrypted, and the hacker then extorts money out of you to get the key. The longer you wait, the higher the price.
Right about now you’re probably thinking, “Not a problem for me, I have backups for all my important files!” Which is good. You can reformat your computer, restore your backups and be done with it. Lesson learned. If you’re not backing up your computer files, now’s the time to start, right? Right? Get started. Seriously.
If that wasn’t bad enough, the people who write ransomware have now figured out how to encrypt your website files and hold them for ransom, and compromises are spreading rapidly across the web. The compromise is done through vulnerabilities in third party applications or your own scripting (out-of-date WordPress sites are a common target – update your WordPress site, plugins and themes!).
At the time we’re writing this, that ransom starts at around $175, and goes up from there the longer you wait. The best way to guard against that is the same way you’ve guarded against site compromise forever: keep your third party application updated, and examine your own code for vulnerabilities.
But if the bad guys do get in and your site files are encrypted and held for ransom, what can you do?
Well, we make site and database backups every day, so we may be able to help you restore the unencrypted version of your files. But our backups are meant for disaster recovery, so there’s often a fee involved with pulling and restoring a copy, and it will take a little time. In addition to that, we only keep a few days of backups. If you don’t notice a ransomware compromise for four or five days, all of our backups will probably be copies of the compromised files, and therefore not useful in restoring the site.
The best answer is maintaining a tight ship, as far as your site is concerned. But a really good standby strategy is our SiteBackup service. It allows you not only to back up website and database files, but to keep multiple versions of those backups for long periods of time. That increases the likelihood that you will have a “clean” backup to restore to defeat the ransomware goons. The best part is you control the backups, they’re available to you immediately any time you need them.
Another cool thing that SiteBackup can do is alert you if Google flags your site as compromised, and automatically disable any further backups. That means you can rest easy that you’ll always have a clean backup for restoration.
Any way you slice it, it’s better to be safe than sorry, so we really recommend checking out SiteBackup. It’s inexpensive (starting at $2.95 a month for 10GB of backup space!), extremely easy to use, and – we think – some of the best peace of mind money can buy.
Activate SiteBackup in Control Panel now.
Here’s what a site compromised by CTB-locker looks like:
No responses yet