
Lately, we have been seeing a higher number of DotNetNuke (DNN) sites getting hacked via a known Telerik.Web.UI.dll vulnerability that’s been around for years. DNN released a patch a few years back. However, we have been seeing in influx of compromised DNN sites caused by this easy-to-fix vulnerability.
If you’re using DNN Versions 5.6.3 through 9.0.1 you must apply this patch to avoid disruptions to your site. More importantly, prevent it from getting hacked.
If you are running a DNN site and need help or want us to patch DNN for you, stop reading and contact our support department. We can help you apply this patch to your site at no cost. Please note that if your DotNetNuke site requires upgrading, then we can help you with that but we do charge for upgrading services.
First thing you need to do is download the patch directly from the DNN Site here: Critical Security Update September 2017
Once you have zip file from the DNN Site, you need to install it as you would an Extension within DNN.
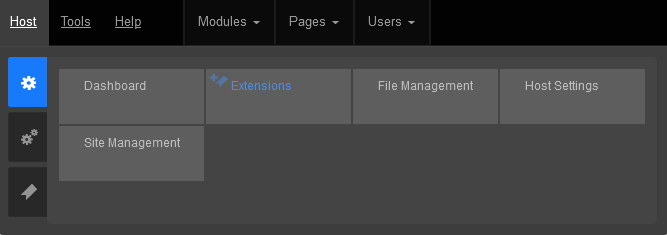
Log into your DNN site as the SuperUser default login.
Navigate to: [HostingAccountDomain.com]/Admin/Extensions
Or look for the Extensions link within your DNN Site.
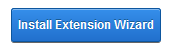
Click on the Install Extension Wizard button
Select Choose File button and select the zip file you just downloaded from DNN in Step 1 and click Next
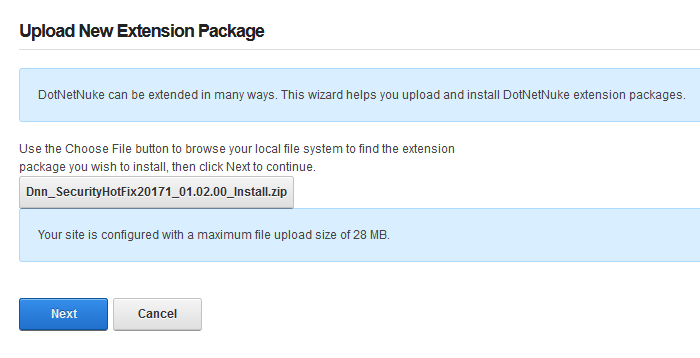
If you receive a random 500 or 404 error within your DNN site after clicking Next from Step 5. Please note the following, otherwise move on to Step 6 below.
You most likely received this error because you need to increase your maxRequestLength setting within your web.config file. You can access this file via FTP.
Look for the setting: maxRequestLength=”12288″
And change it to: maxRequestLength=”28000″
The above increases the limit to 28 MB.
Save your changes and upload the updated web.config file into the same directory overwriting the old web.config file.
Then try Step 5a again.
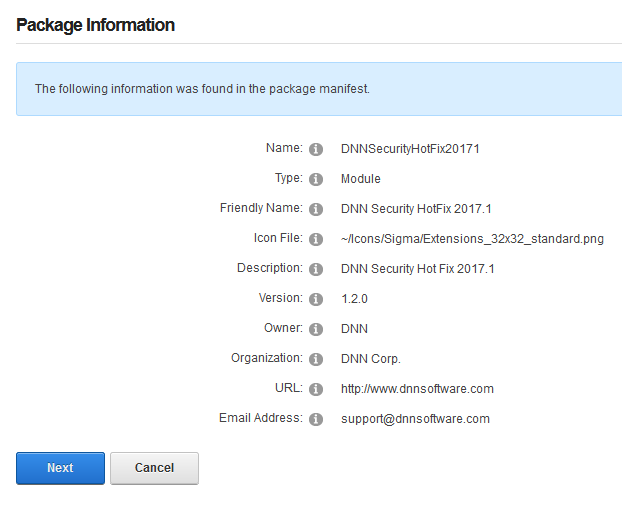
You will see the Package Information about the HotFix. Go ahead and click on Next.
Click Next on the Release Notes window

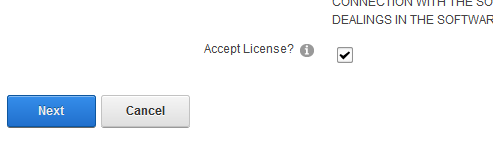
Read and place a check next to Accept License
Click Next.
You will then see the Package Installation Report. Click on the upper right X to exit out of the window.
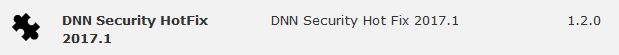
Once your extension page is reloaded. You will see the newly installed Patch for your site.
If you are using DNN, make sure to look into this. There are hackers out there that are targeting DNN and we don’t want you to be a victim of their malicious activities.
If you have any questions or concerns, just contact us.


Many of you are using Microsoft’s Office 365 services for your business or for your personal convenience.
We introduce a new O365Backup service to backup Office 365 – a comprehensive solution to backup Office 365 email, attachments, calendar, contacts, tasks, OneDrive, SharePoint, Groups and Teams.
Automatically Backup Office 365 Content Securely
You can easily set up automated backups for your Office 365 content. Your Office 365 data is secure during transit and your data is encrypted at rest.
Search and Restore Tools are Available
Tools are available in a separate O365Backup Control Panel to search your Office 365 archive and you can restore content from your backup archive.
A Cost-Effective Solution – Unlimited Storage + Unlimited Retention
O365Backup starts at $3.34 per month with unlimited storage and unlimited retention.
FREE 30 Day TRIAL
If you want to test the Office 365 backup service, no problem. We’ll give one user a 30-day FREE Trial so you can test it out and make sure the solution works for your needs.
WordPress is one of the most popular applications on the web with over 74 million installations – that’s a staggering 35% of all the active websites! Unfortunately, with its massive install base, it is natural for hackers to focus a lot of attention on hacking WordPress sites.
In this post, I’ll describe the most common attacks and what you can do about it to lessen the probability of being a victim.
In general, we have found that hackers compromise WordPress installations mostly by one of the two following methods:
Hackers operate many bots that worm through sites and test random login and passwords in the WordPress Admin page.
To get an idea of the scale of attempted logins we’ll take a look at some stats from our own infrastructure. At Winhost, we deploy an Intrusion Prevention System (IPS) on the network edge to detect many malicious activities and try to stop hackers before requests hit our servers. We have rules deployed on the IPS system to thwart Brute Force attacks. However, we cannot make the rules too aggressive because then it can block legitimate requests. It’s a delicate balancing game which we tweak constantly.
Based on the statistics of our IPS system, we typically track 9-10 million WordPress login attempts a month (both malicious and legitimate attempts). Check out the plot below.

About 20% of these attempts are blocked by our IPS system.
2. Outdated Plugins / Themes
Many WordPress sites use various plugins and themes to enhance their sites. The problem is that many plugins and themes have security holes that allow hackers to upload malicious files to the server without the need to log in as an administrator. As a result, we constantly see malicious bots testing for these plugins.
What does Winhost recommend to protect your WordPress site from getting hacked?
Credential Security
<?xml version="1.0" encoding="UTF-8"?>
<configuration>
<system.webServer>
<security>
<ipSecurity allowUnlisted="false">
<add ipAddress="1.2.3.4" allowed="true" />
</ipSecurity>
</security>
</system.webServer>
</configuration> PHP Version
Set your site’s PHP version to 7.1 or above
Update WordPress Frequently
Backup Site and Database
We recommend that you backup your site and MySQL database. We recommend you keep at least 2 weeks worth of backup because you may not realize your site is hacked immediately. Don’t rely on Winhost’s nightly backups because it will only store about 3 days worth of backups. You can automate the backups by using our SiteBackup service.
SiteLock Security service
Consider subscribing to SiteLock Premium or Enterprise Service and enable SmartScan. SmartScan will check your site daily for malicious files and also report on newly created files.
What we do at Winhost to protect your WordPress site
Visit Winhost to learn more about our WordPress Hosting solution

When you are in a bind to find missing website files, the last thing you want to hear from your hosting provider is “Sorry, we don’t have backups of XYZ.”
At Winhost, we do have a backup system in place to backup our customer’s website files and databases nightly. However, this backup system is intended for disaster recovery. We can pull files out of the backup system but this should not be your only backup source.
There have been times when I’ve had customers ask for certain files from our backups, and for one reason or another we didn’t have them because…
In short, there are many different reasons a hosting provider may not have specific backups.
First off, if you haven’t already, download your website to your own computer. If you have any questions about downloading your website files or databases, let us know and we can help. You may want to get on a schedule to download your site every so often. For extra safety, you can copy the files to an external harddrive.
When you are making changes to your site, it’s always best to make the changes on your own computer and then upload the modified files to the webserver. This way you should have the latest copy. Keep in mind that making changes directly on the server may be convenient, but your local copy will be out of sync.
For those that prefer an automated solution for backups over manual methods, we launched our SiteBackup Service.
If you want to make sure your website files and databases are being backed up – nightly, weekly or what ever your heart desires – then our SiteBackup service is a great way of automatically backing up your website and databases. And to protect you further, the backups are not located in the Winhost data center – they are on the Amazon cloud.
In addition, you get a separate control panel for your backups and the backup control panel is located outside of Winhost data center as well.
We have instructions in our knowledge base on how to configure SiteBackup. But if you want our support department to help you set up the SiteBackup service, just let us know after you order. We’ll help you set it up for you.
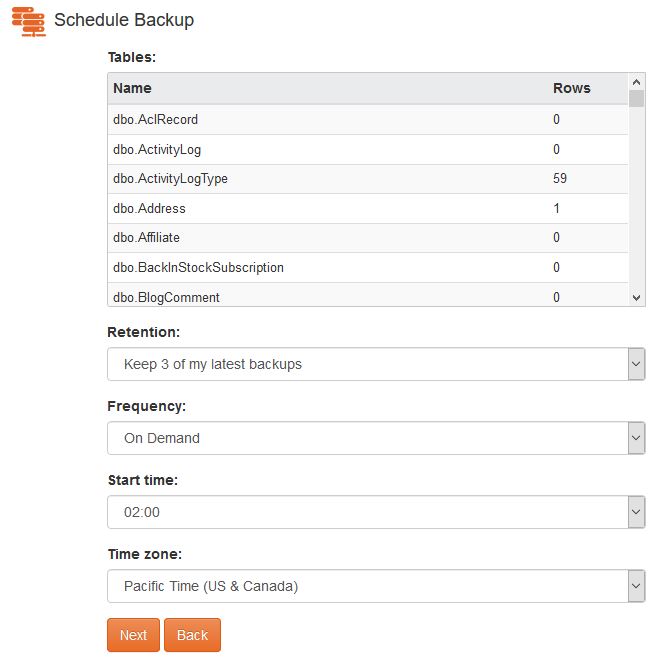
Below is a screenshot of the SiteBackup configuration options.
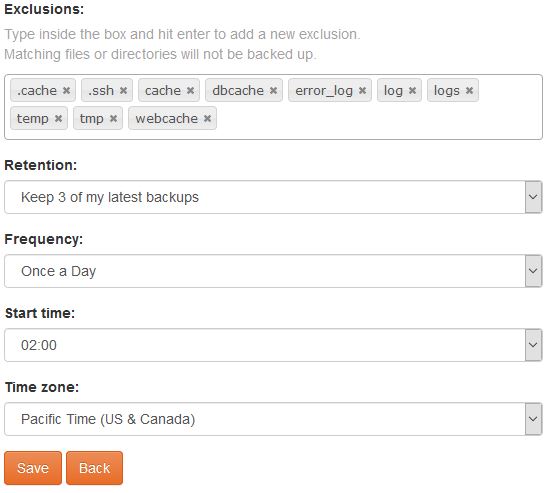
Some of the things you can configure are:
You can backup your MS SQL databases and MySQL database too.
For your site files there is an option to simply restore within the SiteBackup service.

As well as an option to download the site files in zip format.
So the SiteBackup solution is a convenient way to take charge of your site backups. You can sign up for the SiteBackup service through your control panel. If you need help setting it up, just contact our support department. We can help set it up for you.


Email is a vital form of communication and many customers have asked us about Email backups. So we are happy to introduce a new service, EmailBackup!
You Can Automatically Backup Any Email Box
You can easily set up automated backups for your email and attachments. You can backup your email from Winhost email servers or virtually any other email boxes you have elsewhere.
It’s Secure
The email backup storage is secure and encrypted and is also secure during transit.
You Can Easily Search and Restore
Tools are available to search your email archive and you can restore any email messages from your backup.
Manage Your Backups In a Separate Control Panel
The EmailBackup portal is a separate control panel from the Winhost Control Panel and lives outside of Winhost infrastructure. So in the event your Winhost Control Panel is down for any reason, you still have access to your Email backup storage.
A Very Cost-Effective Solution
EmailBackup starts at $1 per month. Peace of mind for less than a cup of coffee! And to sweeten the deal even more, we are offering EmailBackup for 30 days FREE so you can test it out without any risk.
Get Started with EmailBackup Today
30 Days FREE
Click here for more information about EmailBackup from Winhost
As we move into 2020, in this post we do a quick look back on 2019. Here are some of the features, services and enhancements that we introduced in 2019.
Power Plan
Based on customer comments and feedback, we launched our fourth Power Plan to help address the realities of evolving application requirements for modern applications that are consuming more server resources.
SQL 2017
We launched SQL 2017 as a new option for SQL Hosting.
.NET Core and ASP.NET Updates
We try to keep up to date with the .NET Core updates – so we introduced support for .NET Core 2.2 and .NET Core 3. You can always check our knowledge base for the .NET Core versions that are installed on the server. And if you don’t see the .NET Core version you are using, you can use Self-Contained deployment. We also added ASP.NET 4.8 support.
PHP 7.3
We added support for PHP 7.3. Moises even tested if PHP 7.3 runs faster on Windows Server as reported.
Application Installer Updates
We updated the application versions in our App Installer solution within our Control Panel. You can always check the application versions that are being installed with our application installer in our knowledge base.
Thank You for hosting with us!
We are honored that you trust Winhost with your websites, databases and applications. We wish everyone a very Happy New Year!
Visit Winhost to learn more about our ASP.NET hosting solutions
First of all, I want you to understand this email message you received is nothing but a scam and you weren’t really hacked. I’ll explain in more details as you read on.
This is by far one of the best spam email messages I’ve seen since I started working here at Winhost. Not only is it creative but some people are really paying bitcoins to not get “exposed.” That’s why this scam is popular.

Why are people falling for this scam?
This scam is often effective because the email message may contain your real password that you are using. Or, it may contain part of a password that you used in the past.
Or
The email states that the email message was sent from your email account to make you believe that your email was hacked. They may use the following text in their email message to you:
“I’m a programmer who cracked your email account and device about half year ago.
You entered a password on one of the insecure site you visited, and I catched it.”
“I have very bad news for you.
17/07/2019 – on this day I hacked your OS and got full access to your account [email protected].
You can check it – I sent this message from your account.”

The hacker goes on to claim that they installed a Rat program on your computer and no matter what you do, you won’t be able to stop them unless you pay up. Don’t pay them anything. I’ll tell you why…
You might be asking… “well… How did they get my password?“
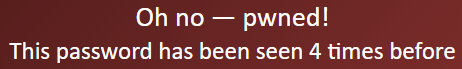
Well you probably heard of all of those nasty data breaches that have been reported on the news and all over the internet? If you were not aware or if you have no idea how anyone might have gotten your account information, there is a website that you can use to check your email address – or any known passwords you like to use and see if it’s part of a data breach. The website is called, “have i been pawned?“. This website’s main purpose is for ordinary people to visit and check if their information was part of any data breach. More about the creator can be found here.
Should I really use this website?
Well, the email message you received already contains your single plain text password. Your password has obviously been compromised before and checking how the hacker may have gotten it can’t hurt you at this point. The hackers also have the same tool to check your password. Hopefully, you are not using that password no more. If you are, change your password.
In the website, you enter the password that you received in the spam email. Their search will bring up what company or list contained that same password.
If your password was compromised, you will get the following message.
“But, they sent me an email from my own email address. So how did they do that?”
Glad you asked. We need to check the email headers and check to see exactly where the email message come from. To get your email header we have the following knowledge base article that shows you how to retrieve this information. An email header may look ugly to a lot of people, but the coolest part is that it tells the story of how you received that email message. Email headers tell a story of the path the email took to get to your inbox.
The email header can be a little tricky to read but you can use some tools to decipher the email header.
The What’s my IP website has the ability to tell you the origin of the email message. Simply copy and paste the email header into the empty field.
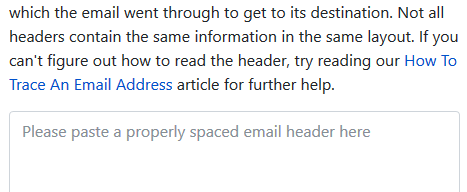
Once you paste in the email header, click on the blue Analyze button. You will get the results of the originating IP number. This is the IP number of the mail server that sent out an email message.
You can check if the IP of the mail server is the same IP number or company that you’re using for your email service. If the IPs don’t match, then the email message has been spoofed – meaning someone just used an email system and changed the “From address” to use your email address. Email addresses are easily spoofed. Just YouTube “how to spoof an email address” if you are interested to learn more.
How do I prevent this from happening again? I hate seeing these damn emails!?
If the email messages you’re receiving are in fact being spoofed, then you have to set up an SPF record and DKIM for your domain name. If you’re using our email services we have the following knowledge base article that provides you with the correct SPF record you should use with our email service.
Is there anything else I can do to stop this email scam?

Yes, we also offer a spam filtering service that stops the bad email messages from ever touching our email systems. The spam filtering service starts to work at the MX level of the email service. This occurs when you change the MX record for your domain name to use the spam filtering service’s MX Records instead. The email messages that are sent to your domain users get routed to the spam filtering service first. Within their system the email messages get scrubbed and filtered and only the legitmate emails get sent to your inbox. Also, a nice feature that comes with our Spam Filtering service – if for some reason our mail server has an issue and can’t receive email messages for any reason – the Spam Filtering service holds on to the incoming email messages and sends it to the main mail server once the issue has resolved. Out of all of the services we offer, the Spam Filtering service is by far one of my favorite ones we provide to our customers.
If you have any questions or concerns about any email spam/scams, feel free to reach out to our technical support team.
Visit Winhost to learn more about our Windows hosting solution